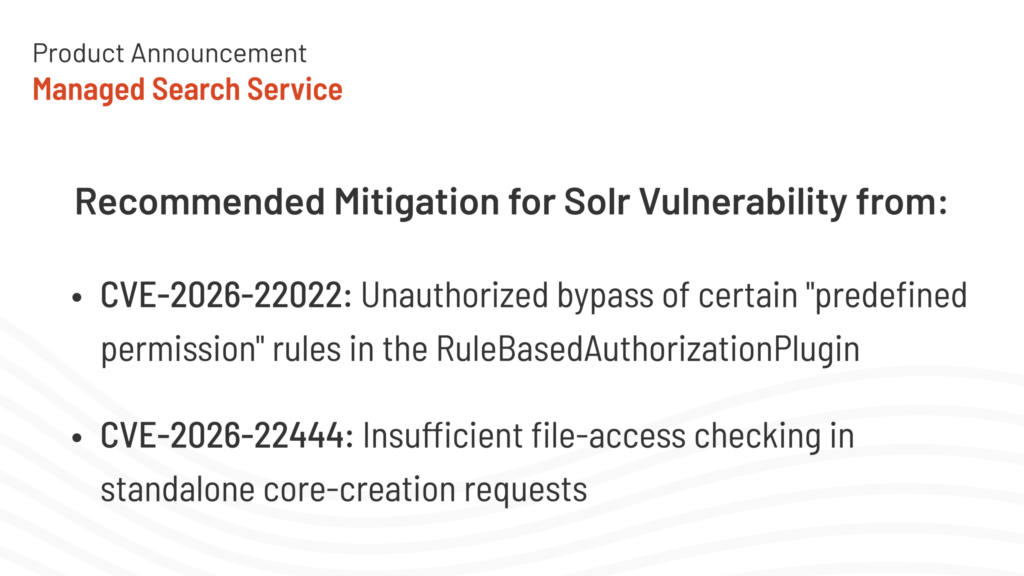
Two new Solr vulnerabilities have been recently identified. One impacts SearchStax deployments. Below we provide the information readily available and the recommended mitigation measures.
This blog’s content will be updated as new mitigation options become available or applied within the SearchStax platform.
This blog’s content will be updated as new mitigation options become available or applied within the SearchStax platform.
Both vulnerabilities have been assigned a Moderate CVSS severity score and are being tracked as CVE-2026-22022 and CVE-2026-22444.
Do CVE-2026-22022 or CVE-2026-22444 affect Site Search?
No.
Site Search does not use Solr in Standalone mode, nor does it use the RulesBasedAuthorizationPlugin.
As a result, Site Search is not vulnerable to CVE-2026-22022 or CVE-2026-22444.
Do CVE-2026-22022 or CVE-2026-22444 affect Serverless?
No.
Serverless does not use Solr in Standalone mode, nor does it use the RulesBasedAuthorizationPlugin.
As a result, Serverless is not vulnerable to CVE-2026-22022 or CVE-2026-22444.
Do CVE-2026-22022 or CVE-2026-22444 affect Managed Search customers?
Managed Search is not vulnerable to CVE-2026-22444 Managed Search does not use Solr in Standalone mode. As a result, Managed Search is not vulnerable to CVE-2026-22444.
For CVE-2026-22022, Managed Search can potentially be exposed to this vulnerability.
Customers running Solr version 9.8.1 and older who are using the Basic Authentication feature and no IP Filtering for their Solr Deployments are vulnerable to CVE-2026-22022.
This vulnerability allows unauthorized HTTP users to be able to read the schema (SchemaHandler) and Solr configurations (SolrConfigHandler) of the various collections on an impacted Solr Deployment.
SearchStax Mitigations & Forward Plan for CVE-2026-22022
- Customers should consider enabling IP Filtering on their Solr deployments for additional security if they do not currently use the feature.
- A patch has been applied to existing deployment to remediate this vulnerability.
- SearchStax has released Solr 9.10.1 so that customers can confidently stay up to date with the latest version of Solr 9.

Get Our Newsletter
The Stack is delivered bi-monthly with industry trends, insights, products and more
Dipsy Kapoor is VP of Engineering at SearchStax, leading teams that build and operate cloud-native search solutions. With a background in search, scalable systems and product engineering, she cares deeply about reliability, relevance, and shipping high-impact features that help customers succeed.