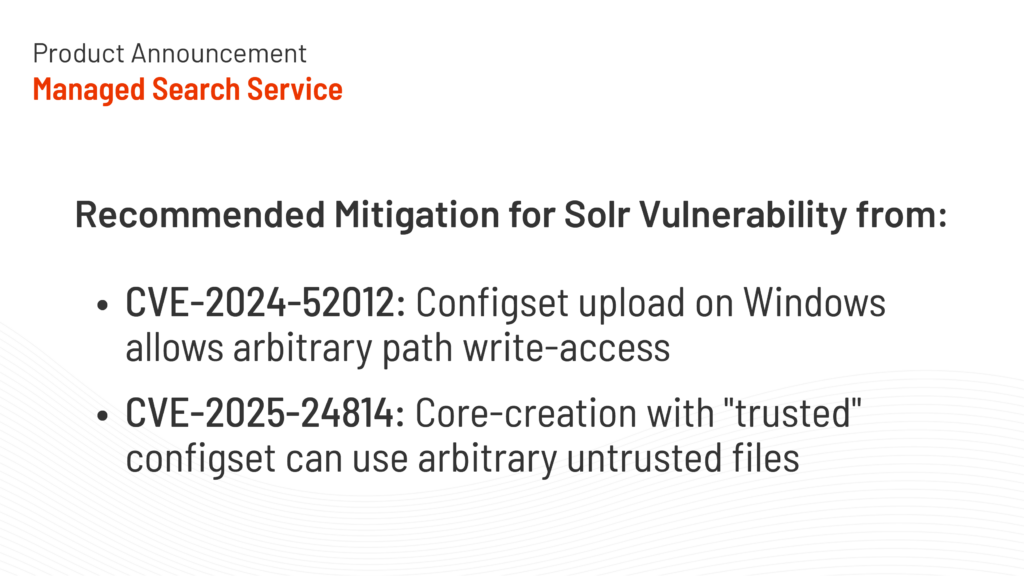
Two new Solr vulnerabilities have been recently identified. We want to provide the information readily available and the recommended mitigation measures as part of providing peace of mind to our customers.
These vulnerabilities have not been assigned CVSS scores yet, and are being tracked as CVE-2024-52012 and CVE-2025-24814.
CVE-2024-52012
Description of Solr Vulnerability
Relative Path Traversal vulnerability in Apache Solr. Solr instances running on Windows are vulnerable to arbitrary filepath write-access, due to a lack of input-sanitation in the “configset upload” API. Commonly known as a “zipslip,” maliciously constructed ZIP files can use relative filepaths to write data to unanticipated parts of the filesystem
Affected Deployments
Deployments using Solr 6.6.0 through 9.7.0 on Windows operating system.
Recommended Mitigations
SearchStax deployments do not run on Windows, so they are not susceptible to this vulnerability.
CVE-2025-24814
Description of Solr Vulnerability
Core creation allows users to replace “trusted” configset files with arbitrary configuration Solr instances that (1) use the “FileSystemConfigSetService” component (the default in “standalone” or “user-managed” mode), and (2) are running without authentication and authorization are vulnerable to a sort of privilege escalation wherein individual “trusted” configset files can be ignored in favor of potentially-untrusted replacements available elsewhere on the filesystem. These replacement config files are treated as “trusted” and can use “<lib>” tags to add to Solr’s classpath, which an attacker might use to load malicious code as a searchComponent or other plugin.
Affected Deployments
Solr Deployments through Solr 9.7.0 running in standalone mode.
Recommended Mitigations
SearchStax deployments do not run in standalone mode and use SolrCloud mode, which is not susceptible to this vulnerability.
Engineering leader building cloud-native search products at SearchStax, focused on scalable systems, search relevance, performance, and delivering outcomes that matter for customers.